 Cloud Storage is best described as data storage that is presented as a service via a network. While the methodology of presentation varies from traditional storage, the implementation of sound and secure practices is key when protecting your critical data. The fundamental and essential practices of patching software, implementing multi-factor authentication, encrypting critical data and instituting the segmentation of your network are all basic building blocks in an overall strategy to protect your most valuable asset, your data.
Cloud Storage is best described as data storage that is presented as a service via a network. While the methodology of presentation varies from traditional storage, the implementation of sound and secure practices is key when protecting your critical data. The fundamental and essential practices of patching software, implementing multi-factor authentication, encrypting critical data and instituting the segmentation of your network are all basic building blocks in an overall strategy to protect your most valuable asset, your data.
1. UNDERSTAND THE RISKS
To establish the proper standards of securing your data it is first necessary to understand the risks that you are faced with. Each year Verizon publishes the Data Breach Investigations Report (DBIR). I highly recommend this as a must read to fully understand the threats and exploits that your organization is potentially exposed. Below, Verizon summarizes the attackers and methods used to exploit a target.
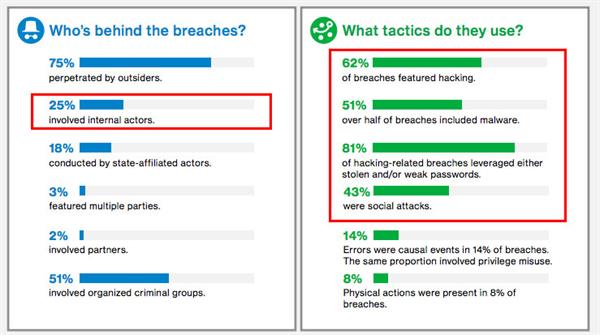
Data Provided by the Verizon 2017 DBIR
As evidenced above, targeting the human factor is still the preferred entry point into your environment. In addition, it is not solely outside hackers IT administrators need to be concerned about, nor one single type of entry.
2. SHARE THE SECURITY RESPONSIBILITY
Security takes a commitment from everyone, not just the security personnel or the IT staff but the entire organization since Malware and Social Attacks are a constant threat. Educating each employee on the proper procedures for handling nondescript email sources and implementing the hardening of passwords are critical in mitigating the origin of breaches from the general employee base. Now that you have addressed the general employee level of exposure what steps can you do to secure your data in the cloud? The idea here is to contain, mitigate and report any form of intrusion.
3. ESTABLISH DATA ACCESS AND AUTHENTICATION POLICIES
First, understand the flow of data for each application. Once you understand the correlation of data to application, you can then implement several key policies that will safeguard your data. Role Based Access is a key step in securing your data and environment. Limiting users to access only the necessary applications and data essential to their job function in essence limits the reach of a rogue employee. As we see in the 2017 Verizon DBIR, rogue employees constitute 25% of all reported breaches. Once role based access has been implemented, take the additional step of leveraging multi factor authentication (MFA). This can come in the form of tokens or other methodologies. The use of MFA will severely limit the access of external forces into your environment. While we are on the subject of roles, it is also wise to disable or limit root or domain admin rights. If this type of account gets compromised then the intruder will have full access to your entire topology.
4. ESTABLISH NETWORK ACCESS POLICIES
Your network should never be flat where any device can access any device. Take advantage of features such as Virtual Local Area Network (VLAN) to segment access and traffic. For example, a person assigned the role of reporting should never have access to the segment of the network where server and data storage traffic is originating. With this concept, you can now create VLANs that allow an employee the proper access to the appropriate resources. You can easily understand that if an employee’s access is compromised the access is contained within a finite section of your architecture.
5. UNDERSTAND YOUR PROVIDER’S SECURITY FEATURES
Before committing to a cloud based storage architecture, discuss the physical security features that your provider has implemented. Ask questions that detail how hardened their access policies are for getting onsite. Keep in mind, securing your data is a partnership between you and the provider. Typical security measures such as firewalls, VLANs and multi factor authentication should be implemented.
6. TAKE ADDITIONAL PROACTIVE STEPS
In addition to these measures, you should consider establishing separate data connections, one to the internet and a second link that will connect to your cloud based assets. You should also include regularly scheduled penetration testing, implementing threat detection devices so you can react quickly to a breach and encryption in transit techniques. Lastly, a well-defined process that implements patches and updates throughout the architecture can be very instrumental in mitigating risks similar to what we saw in the past with the WannaCry ransomware breach.
Realistically, no one can guarantee absolute protection from all threats to your IT architecture and data. However, by implementing a multi-tiered approached beginning with educating every employee on proper security behavior, designing the proper access and configuring a hardened environment, you can be assured of protecting your organizations from most cyber threats.

